The Effect of Effective Data Destruction on Cyber Security Threat Administration
The Effect of Effective Data Destruction on Cyber Security Threat Administration
Blog Article
The Essential Nature of Data Destruction in Upholding Computer System Security Providers and Protecting Against Unauthorized Gain Access To
In an age where data breaches and identity theft are progressively prevalent, the significance of reliable information damage can not be overstated. Various approaches, from data wiping to physical devastation, offer as vital safeguards against unauthorized accessibility.
Importance of Data Destruction
In an increasingly electronic globe, the value of information devastation can not be overstated. As companies generate substantial quantities of delicate information, the possible repercussions of stopping working to properly get rid of and handle of that information end up being increasingly severe. Information violations, identity burglary, and company espionage pose significant hazards, emphasizing the need of reliable information destruction methods.
In addition, as innovation develops, so also do the methods by which harmful stars seek to make use of delicate info. Organizations has to remain alert and proactive in their data devastation approaches to safeguard against these progressing hazards. By focusing on information destruction, companies not only shield their properties however likewise foster depend on among stakeholders and clients, showing a dedication to liable information administration and safety techniques.
Approaches of Effective Information Devastation
To make sure the irreversible and full damage of sensitive information, companies can utilize a variety of reliable approaches tailored to their details needs. Among the most usual techniques is information cleaning, which involves using specialized software application to overwrite existing data multiple times, making recuperation virtually difficult. This is especially useful for hard disks and solid-state drives, where conventional removal techniques are poor.
One more reliable method is degaussing, which uses solid electromagnetic fields to interrupt the magnetic domain names on storage space media, providing the information irretrievable. This method is specifically suited for magnetic storage tools, such as disk drive and hard drives.
Physical destruction is likewise a feasible option, including the shredding, crushing, or incineration of storage tools. This approach warranties that data can not be recouped, making it ideal for companies managing very sensitive information.

Compliance With Data Security Regulations
Organizations have to not only concentrate on efficient data damage techniques but additionally guarantee conformity with information protection policies that govern just how sensitive info is managed and thrown away. Complying with these policies is necessary for keeping and protecting individual information client depend on. Rules such as the General Data Defense Guideline (GDPR) in the European Union and the Health Insurance Transportability and Liability Act (HIPAA) in the USA impose strict guidelines on information monitoring, which include requirements for the safe and secure disposal of delicate details.
To attain compliance, companies should implement comprehensive information destruction policies that line up with these lawful frameworks. This includes recognizing data that needs devastation, establishing methods for protected methodsâEUR" such as shredding physical media or using software that fulfills sector standards for information wipingâEUR" and preserving thorough documents of devastation tasks. Routine audits ought to be performed to guarantee adherence to these policies and to identify any kind of prospective areas for enhancement.
Failure to official site follow information security laws can lead to substantial lawful implications, including substantial fines and damage to an organization's track record. As a result, integrating conformity into data devastation practices is not just a lawful responsibility yet also an essential part of a durable info security technique.
Effects of Poor Data Handling
Poor data handling can bring about extreme consequences that extend past prompt operational setbacks. Organizations might encounter substantial monetary losses due to data violations, which commonly result in costly remediation efforts, legal charges, and governing fines. These economic ramifications can stress sources and prevent development, ultimately impacting a company's bottom line.
Additionally, bad data handling can severely harm an organization's track record. Stakeholders, clients, and partners might lose rely on an entity that falls short to protect sensitive info, leading to lowered pop over to this web-site consumer loyalty and prospective loss of service possibilities. This erosion of trust fund can take years to rebuild, if it can be brought back whatsoever.
In addition, companies could deal with legal implications arising from non-compliance with information protection guidelines. Such infractions might lead to charges and examinations, worsening the financial burden and additional tainting the company's picture.
In the realm of cybersecurity, poor data management practices can develop vulnerabilities that make systems extra vulnerable to unauthorized access and cyberattacks. Ultimately, these effects underscore the critical importance of implementing durable information managing treatments to guard delicate details and keep business integrity.
Best Practices for Secure Data Disposal

Firstly, data must be classified according to its level of sensitivity. Sensitive info requires more strenuous disposal approaches, such as shredding physical files and utilizing innovative software for digital data wiping. Employing qualified data devastation services ensures compliance with sector policies and requirements.
Secondly, companies must implement an information disposal policy that mandates routine audits. This policy needs to lay out the treatments for information retention and devastation, making certain that obsolete information is dealt with without delay and safely. Educating workers on these procedures is vital go to the website to fostering a culture of safety understanding.
Finally, preserving comprehensive records of disposed information boosts liability and gives a clear audit route. This documents must consist of the sort of data destroyed, the technique used, and the day of disposal.
Verdict
In verdict, the necessary of efficient information devastation appears in its function in boosting computer safety and security services and alleviating unapproved access risks. Embracing durable approaches such as information cleaning, degaussing, and physical devastation, together with conformity with regulations like GDPR and HIPAA, is necessary for securing sensitive information. Neglecting proper data disposal methods can bring about serious repercussions, consisting of data breaches and lawful repercussions. Carrying out finest practices in protected data disposal ultimately strengthens organizational honesty and client trust fund.
In an era where information violations and identification theft are significantly widespread, the value of efficient data damage can not be overemphasized. data destruction. Data violations, identity burglary, and company reconnaissance present considerable threats, underscoring the necessity of reliable data damage practices
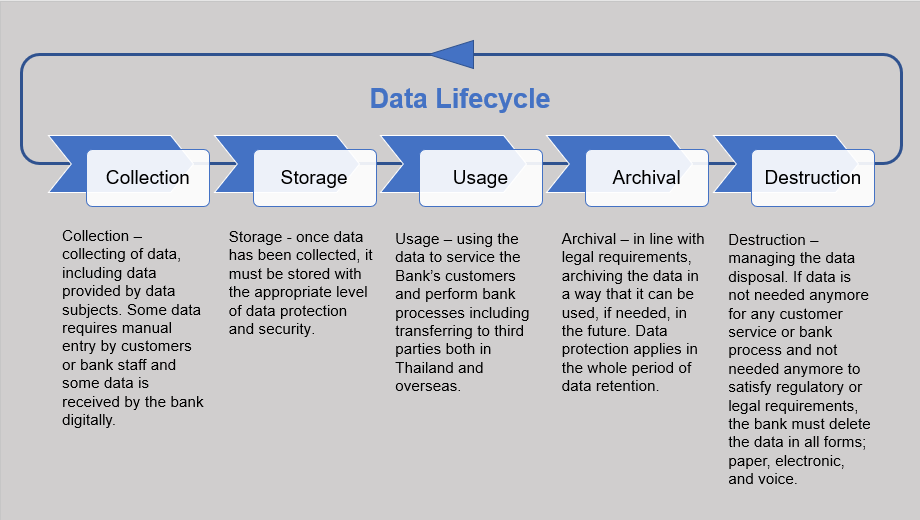
Conformity with guidelines such as GDPR and HIPAA requireds that companies apply rigid data security procedures, including the safe devastation of information at the end of its lifecycle.
By prioritizing data destruction, business not only safeguard their properties but also foster trust fund among clients and stakeholders, demonstrating a commitment to responsible data management and security practices.
Organizations need to not only focus on reliable data devastation techniques however likewise ensure conformity with information defense regulations that control how delicate details is managed and disposed of.
Report this page